Setting Up a G Network for Security Information and Event Management
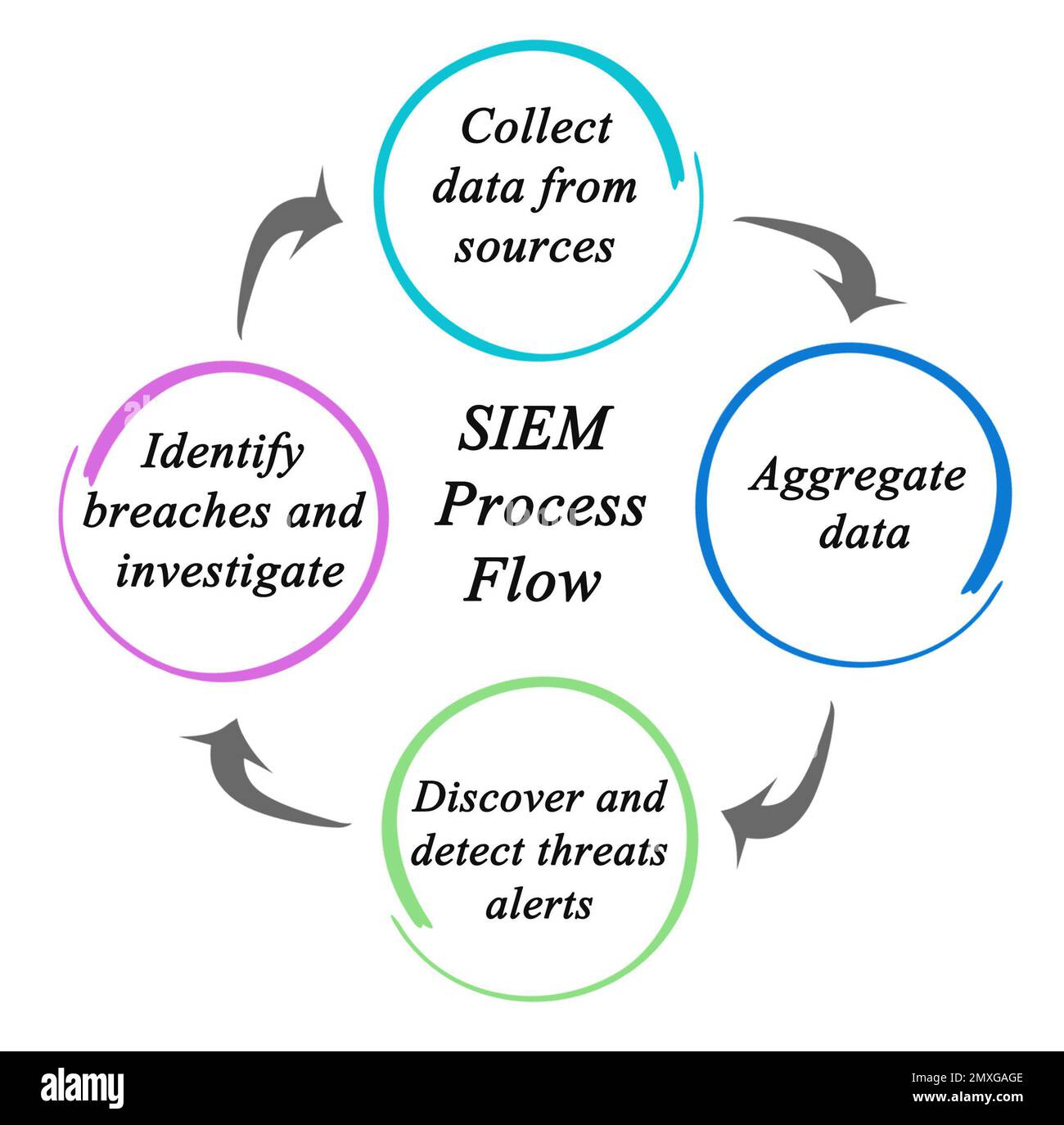
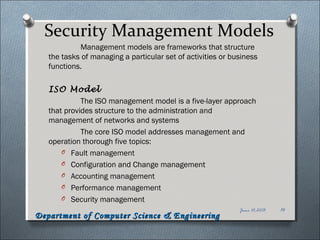
Aug 19, 2025, Security Information and Event Management (SIEM) deployment involves setting up and configuring a system to aggregate security event logs across an organization's infrastructure. This process requires careful planning, selection of the right SIEM solution, and configuration of data collection, correlation, and response mechanisms.
What is SIEM?
SIEM Key Features and Benefits

Such details provide a deeper understanding and appreciation for Setting Up A G Network For Security Information And Event Management.
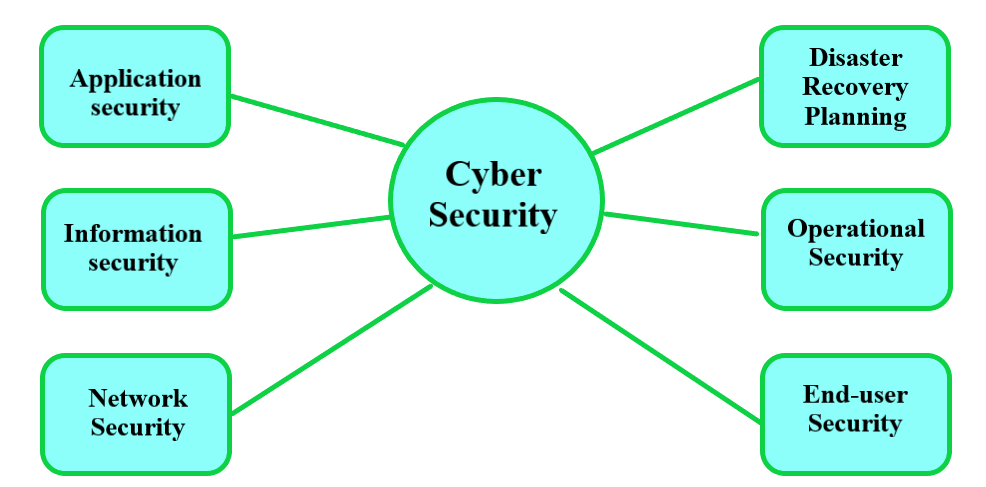
- Real-time visibility**: SIEM provides real-time visibility across an organization's security systems, enabling them to detect and respond to security threats in a timely manner.
- Event log management**: SIEM collects and aggregates log data from various sources, providing a centralized view of security-related events.
- Correlation and analysis**: SIEM uses predefined rules to correlate log and event data, identifying potential security incidents and generating alerts.
- Alerts and dashboards**: SIEM provides customizable alerts and dashboards that prioritize high-risk events, enabling security teams to focus on the most critical threats.
- Integration**: SIEM can integrate with existing security tools and technologies, providing a comprehensive view of security threats and incidents.
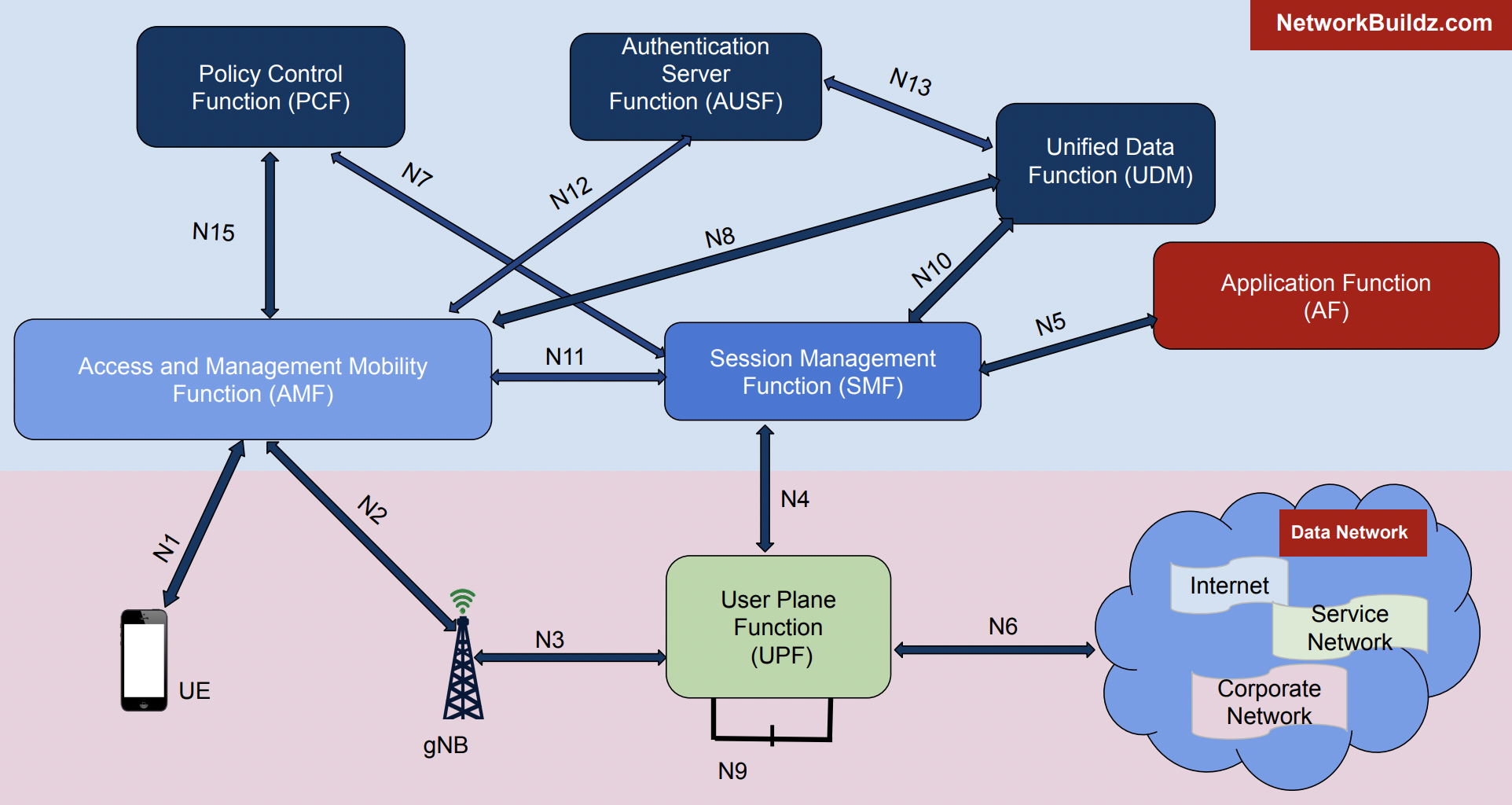
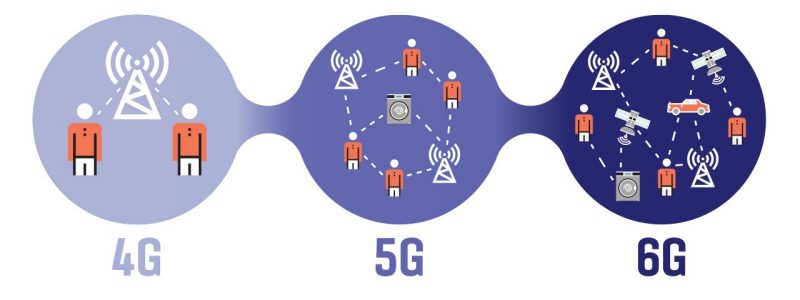
Setting Up a G Network for SIEM
Setting up a G network for SIEM involves several key steps:

Furthermore, visual representations like the one above help us fully grasp the concept of Setting Up A G Network For Security Information And Event Management.
- Planning and selection**: Determine the organization's security requirements and select a suitable SIEM solution that meets those needs.
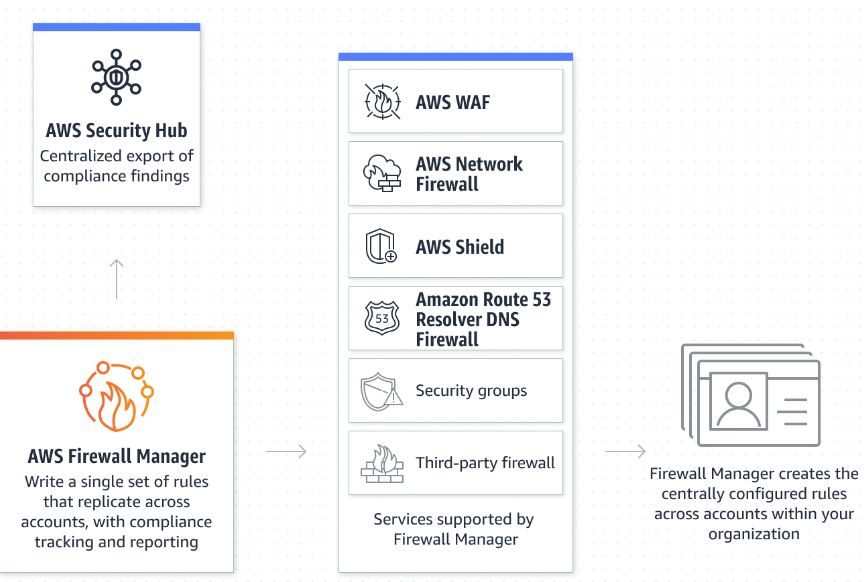
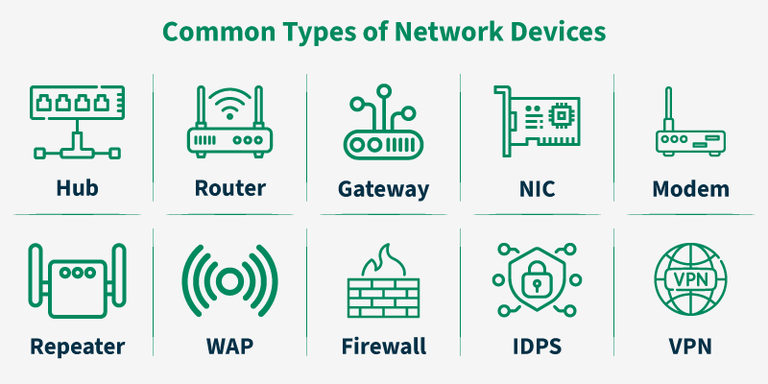
- Data collection**: Configure data collection mechanisms to gather log data from various sources, including servers, endpoints, applications, and network devices.
- Correlation and analysis**: Develop correlation rules to analyze log and event data, identifying potential security incidents and generating alerts.
- Alerts and dashboards**: Configure alerts and dashboards to prioritize high-risk events and provide a centralized view of security threats.
- Integration**: Integrate the SIEM system with existing security tools and technologies to provide a comprehensive view of security threats and incidents.
Benefits of Setting Up a G Network for SIEM
Setting up a G network for SIEM provides several benefits, including:

As we can see from the illustration, Setting Up A G Network For Security Information And Event Management has many fascinating aspects to explore.
Conclusion
Setting up a G network for Security Information and Event Management (SIEM) is a critical step in protecting an organization's security posture. By following the key steps outlined above, organizations can implement a SIEM solution that provides real-time visibility, event log management, correlation and analysis, alerts and dashboards, and integration with existing security tools and technologies.