How to Protect Identity from Complete Messages Operations Ore Re Audit
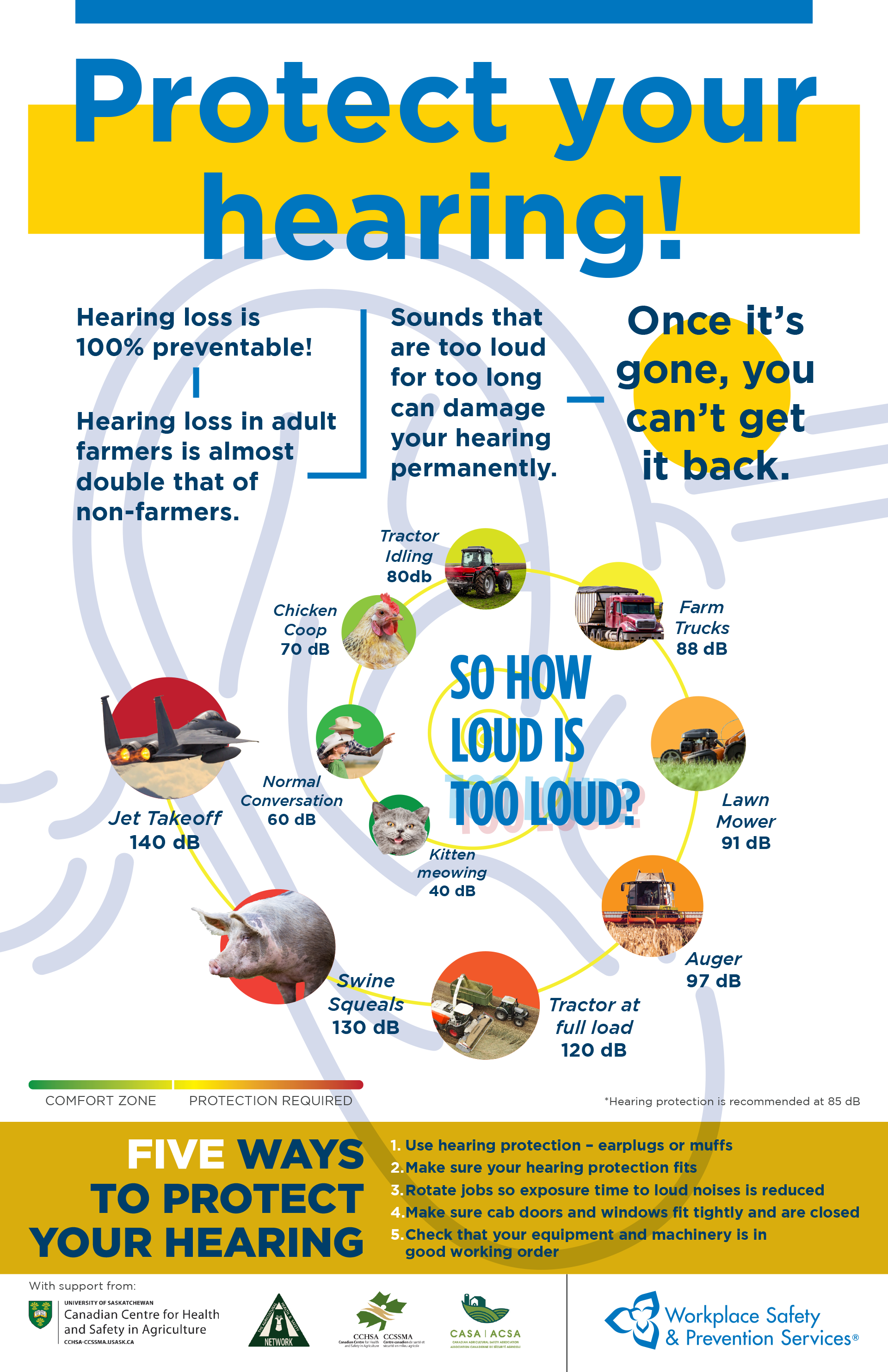
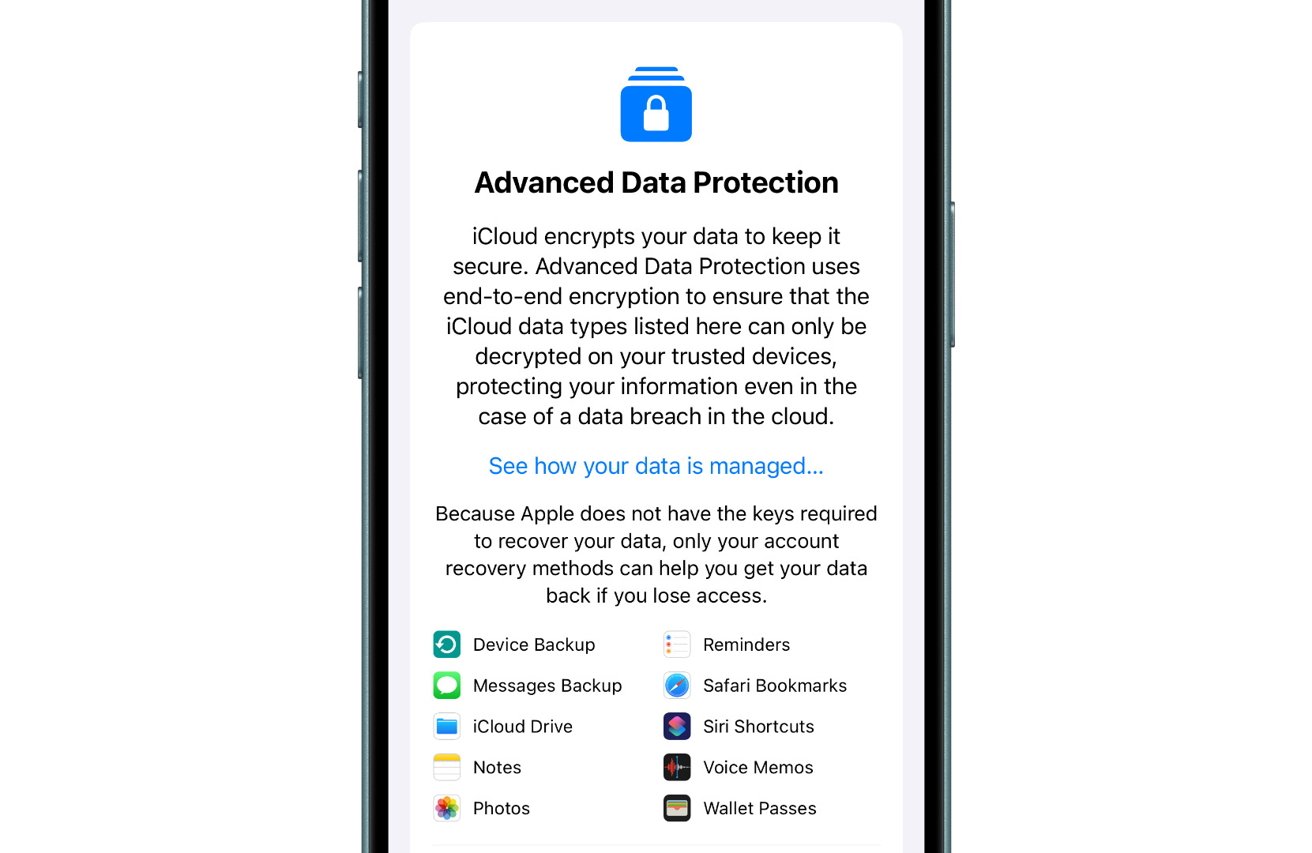
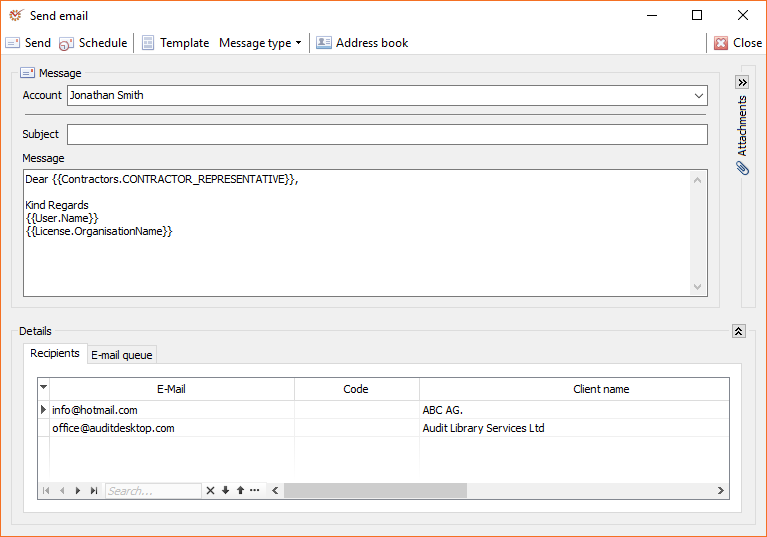
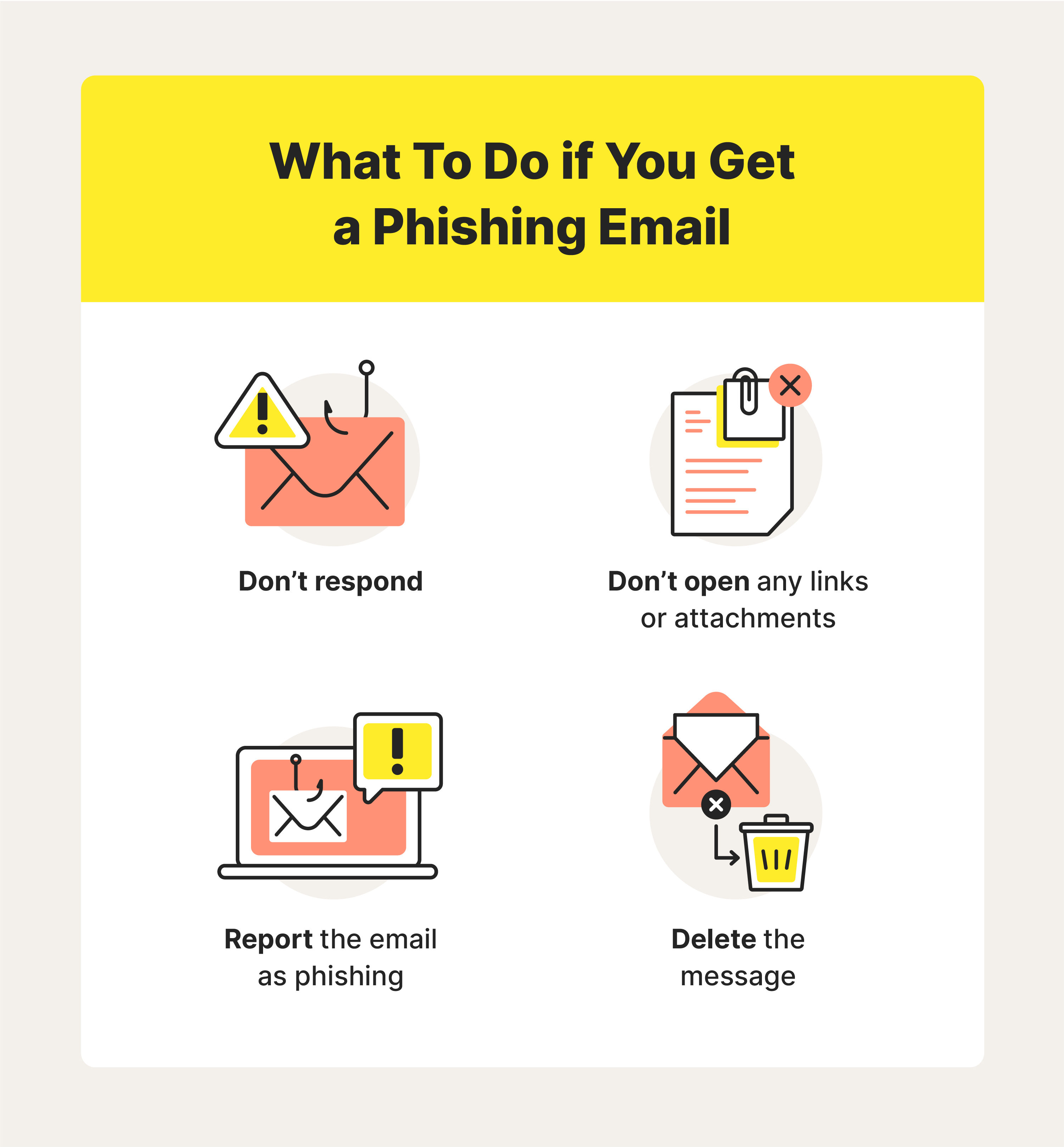
As an organization, faces numerous threats to its sensitive information, including identity theft, data breaches, and fraud. Sensitive personal information, such as names, social security numbers, credit card numbers, and other account data, is widely used in business operations. However, a security audit is a process of identifying, evaluating, and resolving vulnerabilities in an organization's security posture to ensure compliance with information security audit requirements.Why is a Security Audit Important?

Moving forward, it's essential to keep these visual contexts in mind when discussing How To Protect Identity From Completes Messages Operations Ore Re Audit.
A security audit is essential to understand how it affects the management of sensitive information and compliance with information security auditor requirements. By conducting regular security audits, an organization can: * Identify vulnerabilities and weaknesses in its security posture * Develop strategies to mitigate potential risks * Comply with regulatory and compliance requirements * Protect sensitive information from unauthorized access * Ensure the overall security and integrity of the organization's operations8 Checklist Points to Strengthen Your IAM Strategy
Benefits of a Security Audit