G Network Configuration for SSL VPN: A Comprehensive Guide
Introduction to SSL VPN
Benefits of SSL VPN
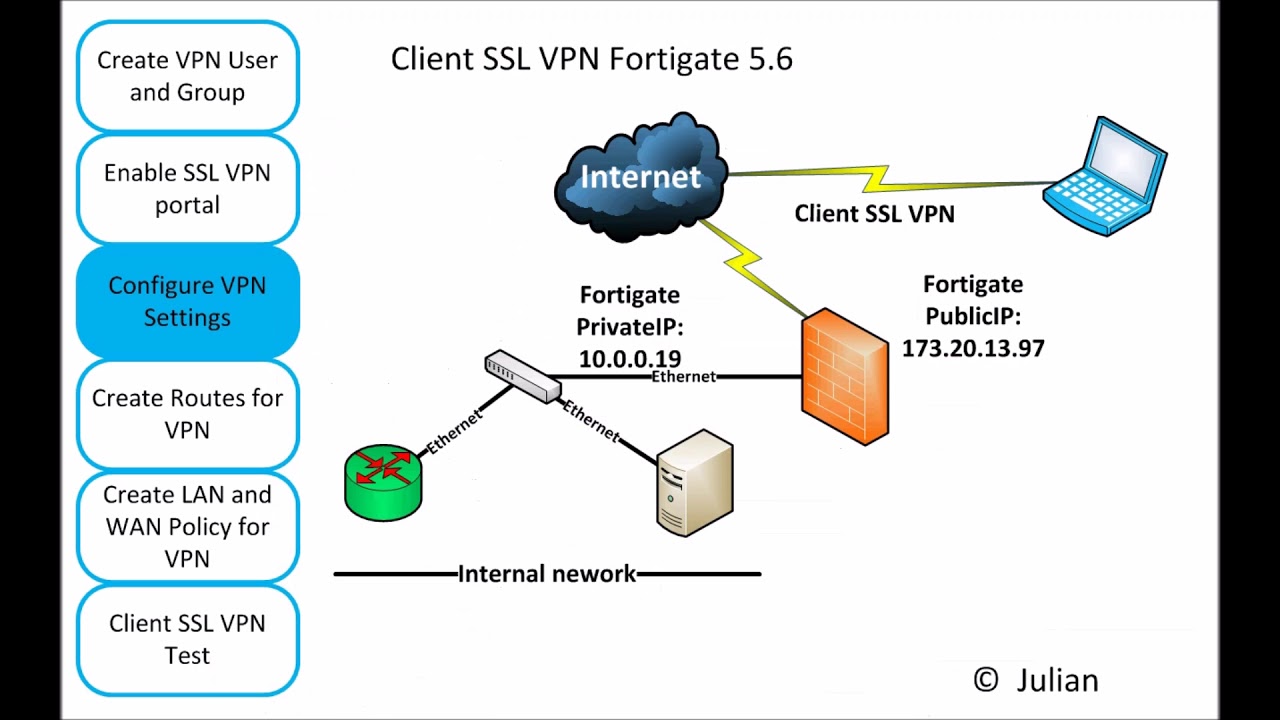
This book explains step-by-step how to configure a FortiGate firewall in thenetwork. Each chapter begins with learning objectives and contains step-by-step explanations for GNS3 beginners on how to build different security scenarios from scratch.
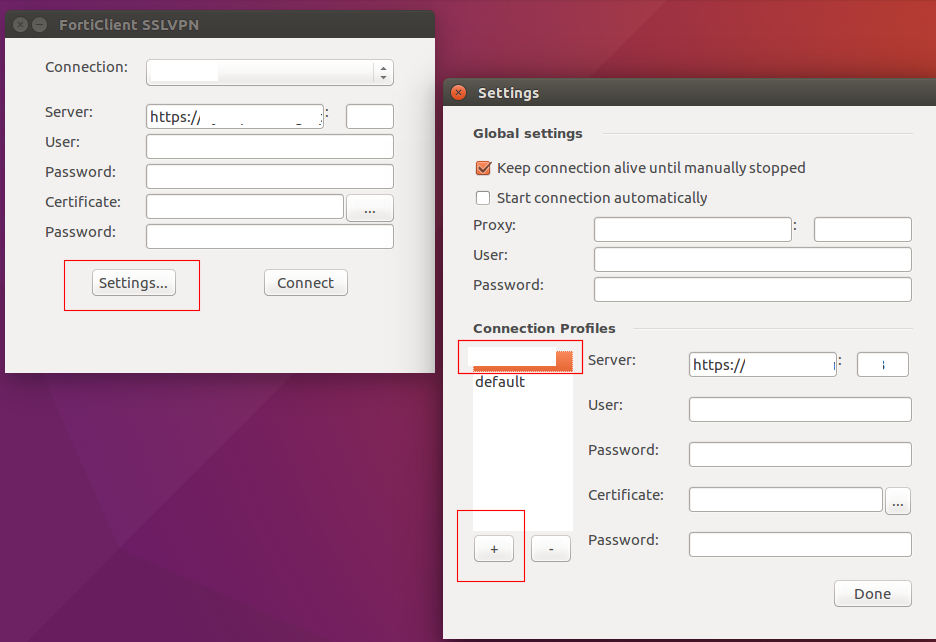
After a few introductory articles that covered user authentication, there is an extensive piece onSSLVPNconfiguration. I tried to make the description very comprehensive, as I find the official documentation insufficient. A few simple steps are all you need to create a basicVPNconnection (examples are in the official documentation). This article should also show all the special options we ...

6 days agoEdit the Nginxconfigurationfile to define theVPNserver's settings, such as the IP address, port, and protocols to be used. Additionally, configureSSL/TLS settings to enable secure communication between theVPNserver and clients.
Sep 22, 2024Learn how to configureSSLVPNin FortiGate with this easy-to-follow guide, ensuring secure remote access for yournetwork.
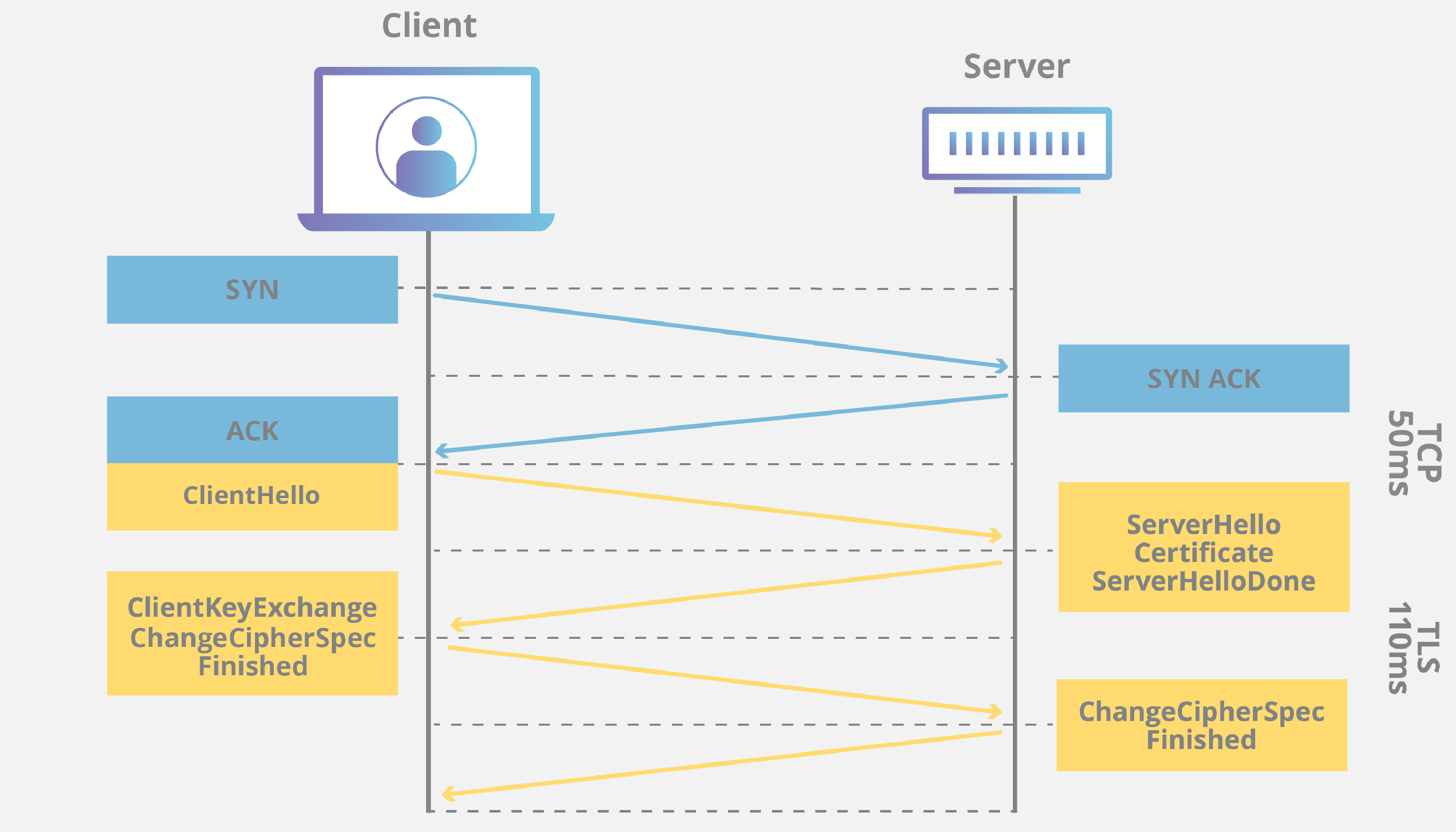
TodayIt fundamentally involves setting up a secure tunnel between a remote user's device and your privatenetwork, all over the public internet, usingSSL/TLS encryption. This guide aims to demystify that process, offering you the insights and steps needed to achieve robustSSLVPNdeployment.
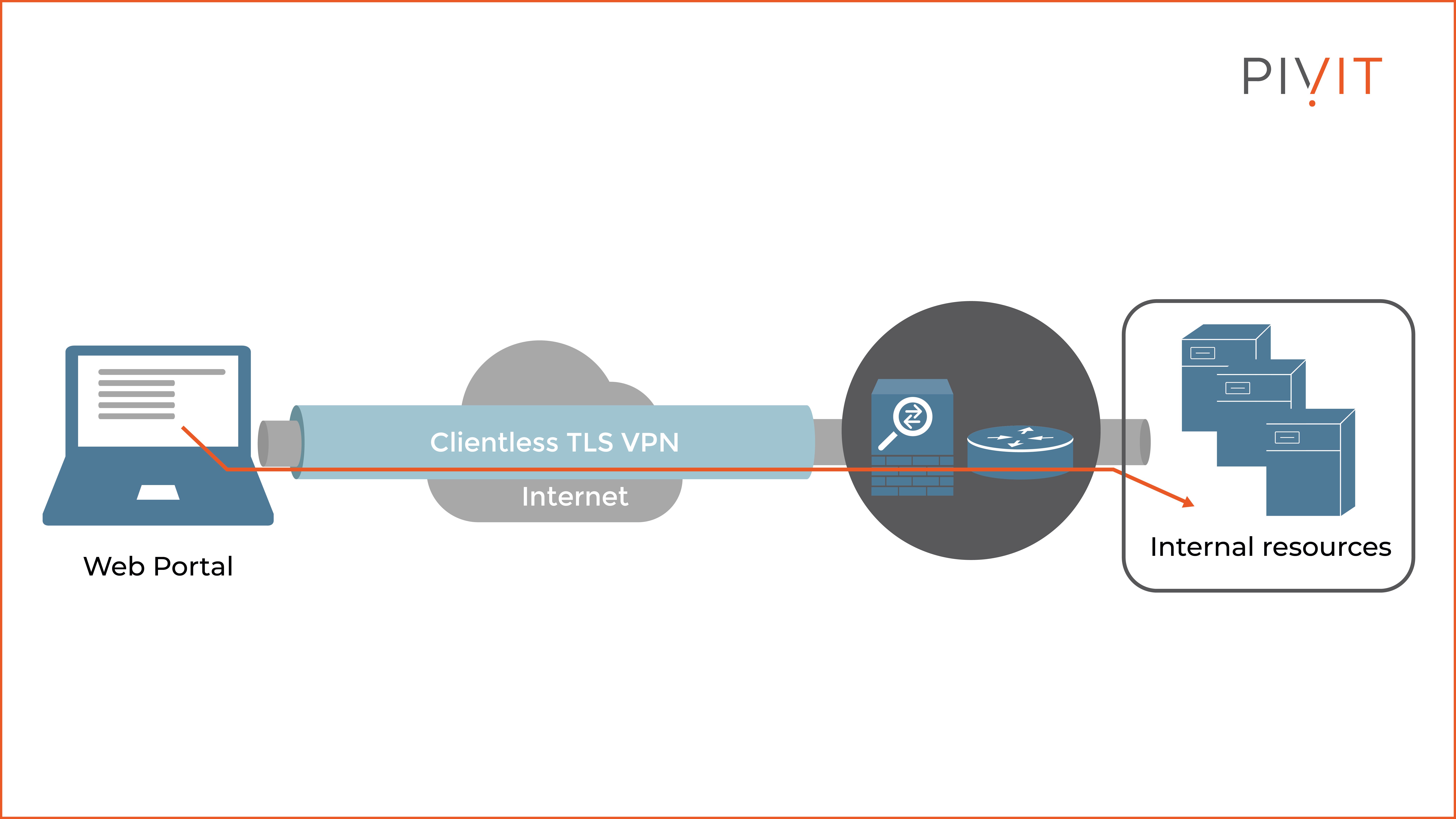
Apr 28, 2024A secure sockets layerVPN(SSLVPN) enables individual users to access an organization'snetwork, client-server applications, and internalnetworkutilities and directories without the need for specialized software.SSLVPNsprovide safe, secure communication via an encrypted connection for all types of devices, regardless of whether access to thenetworkis via the public internet or another ...
Jan 22, 2026How to install and use OpenVPN ¶ OpenVPN is a flexible, reliable and secure Virtual Private Networking (VPN) solution. It belongs to the family ofSSL/TLSVPNstacks (different from IPsecVPNs). This chapter will show how to install and configure OpenVPN to create aVPN. Install the server ¶ To install OpenVPN, run the following command in your terminal:
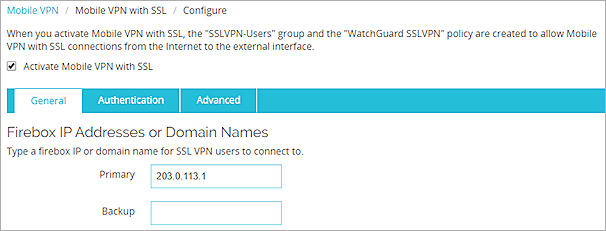
To configure theSSLVPNrealm: Go to System > Feature Visibility. EnableSSL-VPNRealms. Click Apply. UnderVPN>SSL-VPNRealms, click Create New. Enter the URL path pki-ldap-machine. Click OK to save.
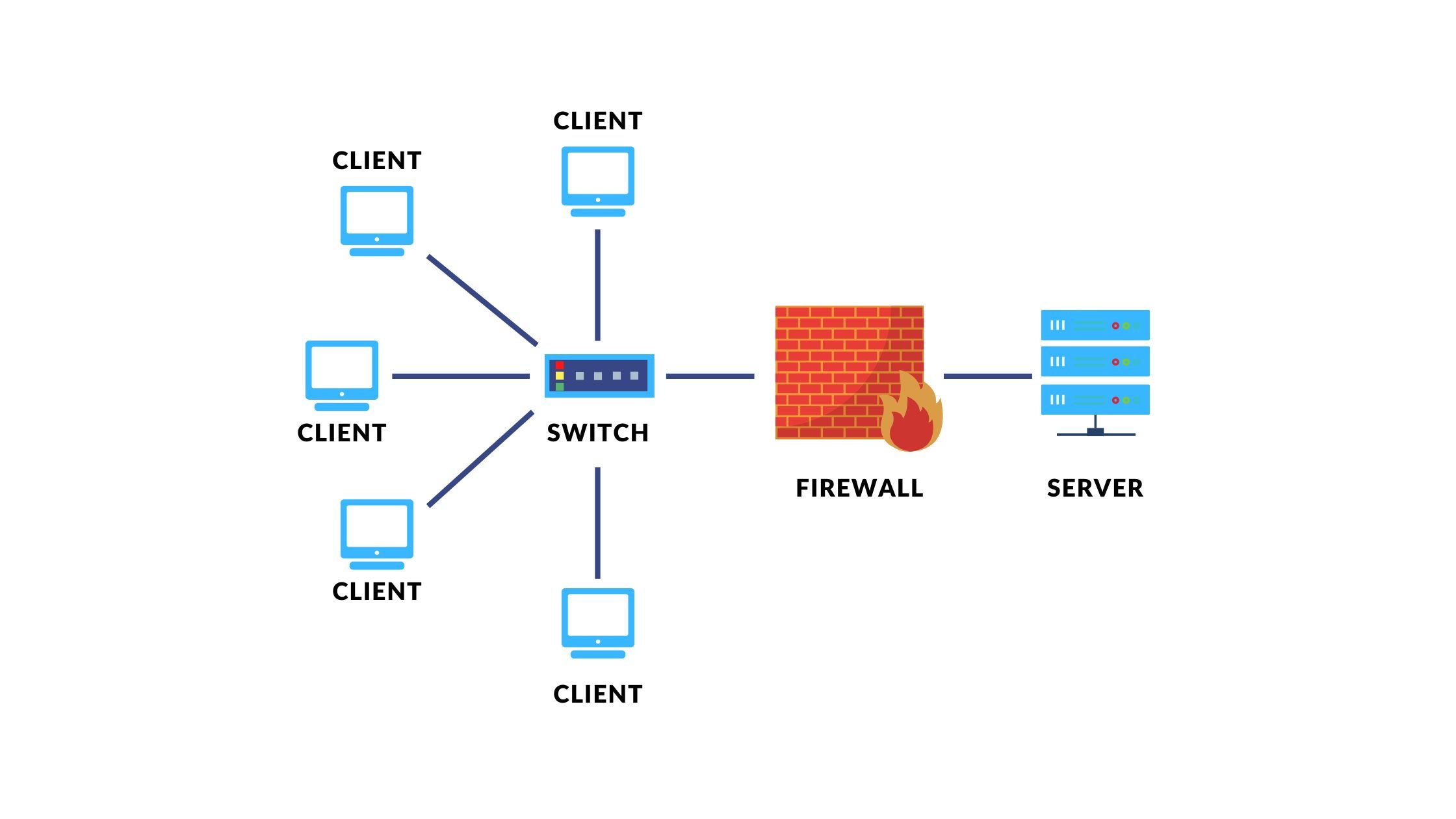
How to prevent the user on the LAN internalnetworkfrom connecting to theSSLVPN/Client itself. We come across this case, where the user should only be able to access anSSLVPN/Client when they are internal, not when they are internal.
Introduction AnSSLVPNis a virtual privatenetworkwhich uses the Secure Layer Socket (SSL) or the Transport Layer Security (TLS) protocol in web browsers to create a secure, remoteVPNconnection between the endpoint device and theSSL/TSL server. Using end-to-end encryption (E2EE), anSSLVPNenables remote users, such as corporate employees, telecommuters, contractors, and so on, to ...

Mar 31, 2025A Virtual PrivateNetwork(VPN) is a secure, encrypted tunnel established over an untrustednetwork(e.g., the internet). It ensures confidentiality, integrity, and authentication between endpoints.
CISA

How to prevent the user on the LAN internalnetworkfrom connecting to theSSLVPN/Client itself. We come across this case, where the user should only be able to access anSSLVPN/Client when they are internal, not when they are internal.
Select NetworkGlobalProtectGateways to configure a GlobalProtect gateway. A gateway can provideVPNconnections for GlobalProtect apps or for GlobalProtect satellites. From the GlobalProtect Gateway dialog, Add a new gatewayconfigurationor select an existing gatewayconfigurationto modify it.

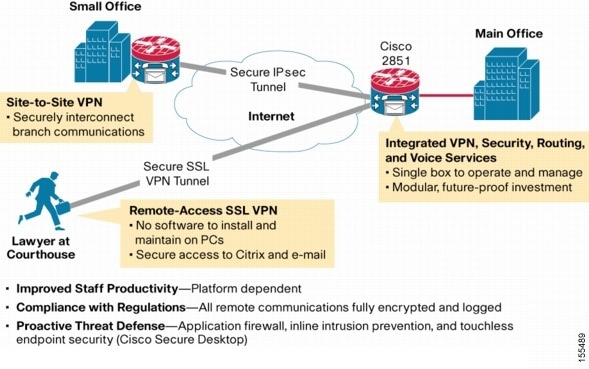
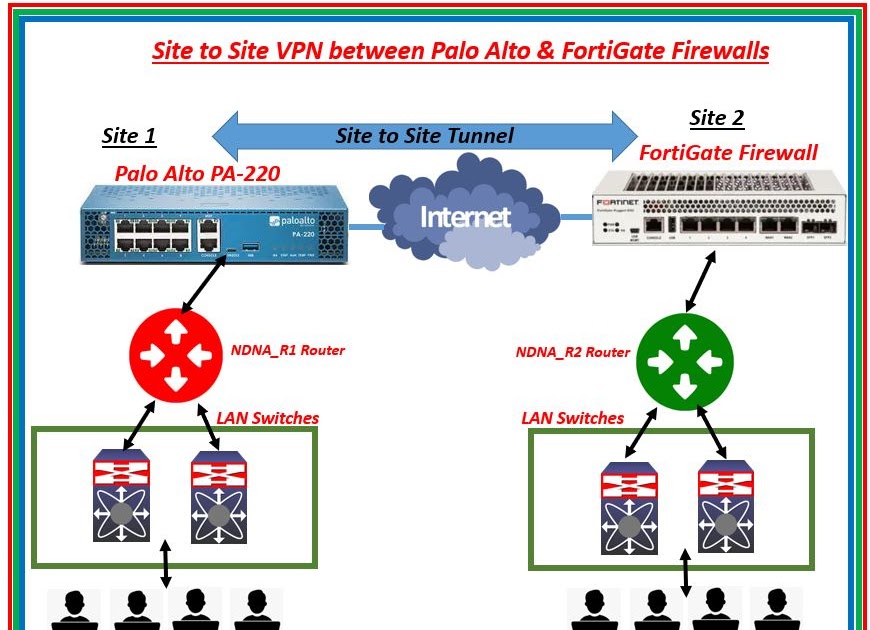
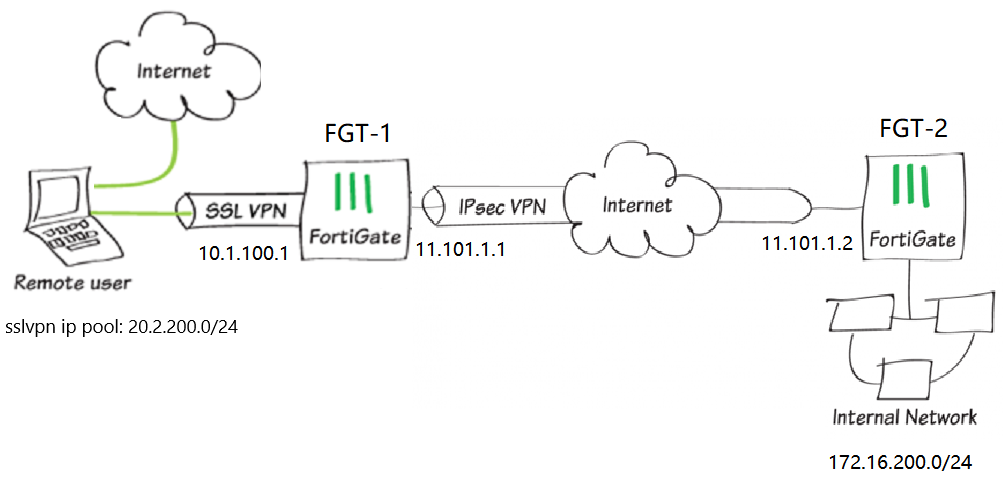
1 day agoWhat is the difference betweenSSLVPNand IPsecVPN? IPsecVPNoperates at thenetworklayer (Layer 3) and is typically used for site-to-site connectivity between fixed locations. It encrypts all IP traffic between definednetworkranges and generally requires aVPNclient or compatible router at both ends.SSLVPNoperates at the application layer using TLS encryption and is designed for ...

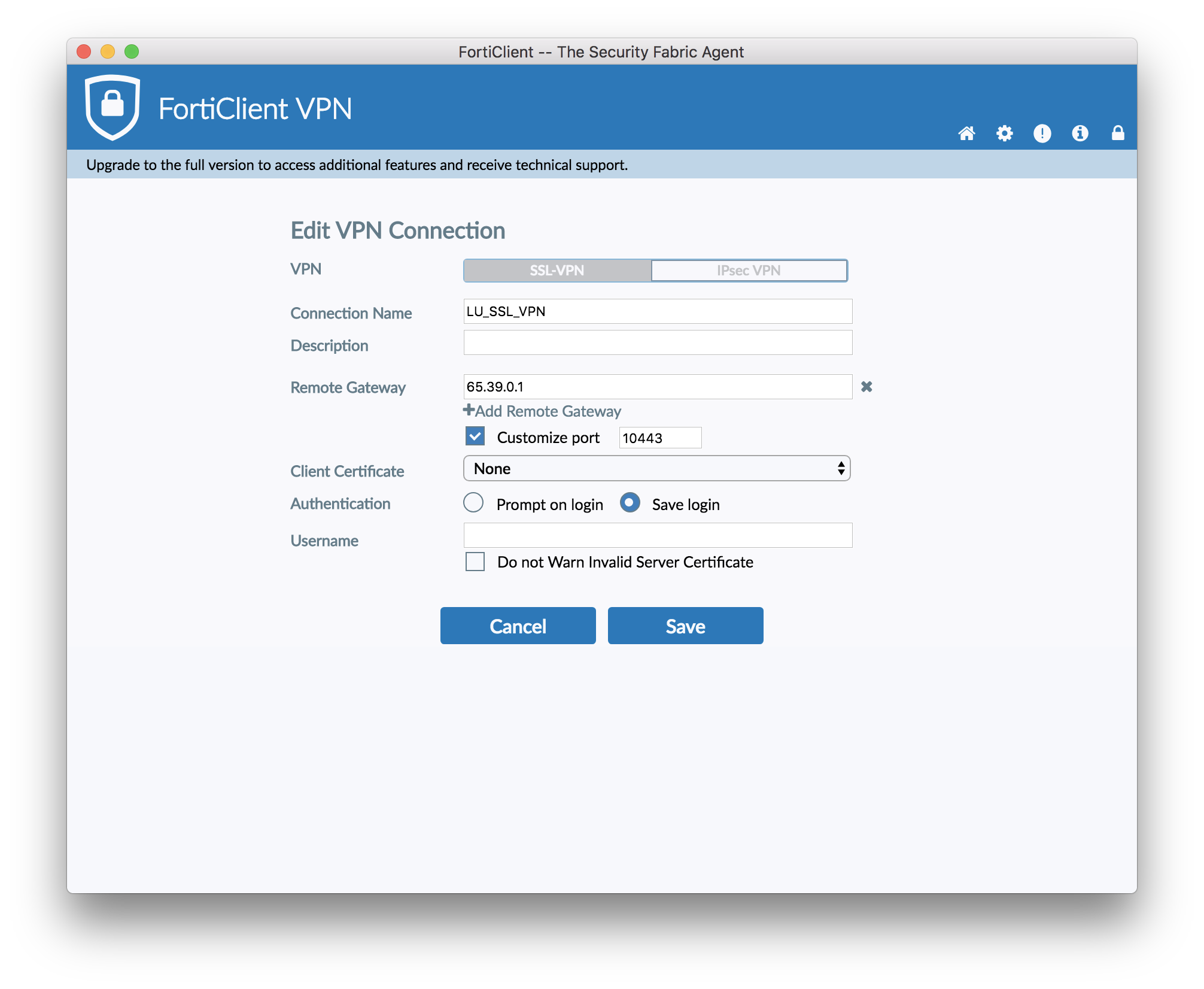
Configuring anSSLVPNconnection In FortiOS 7.6.3 and later versions,SSLVPNtunnel mode is no longer supported andSSLVPNweb mode is renamed to "agentlessVPN". See Migration fromSSLVPNtunnel mode to IPsecVPNand AgentlessVPN.
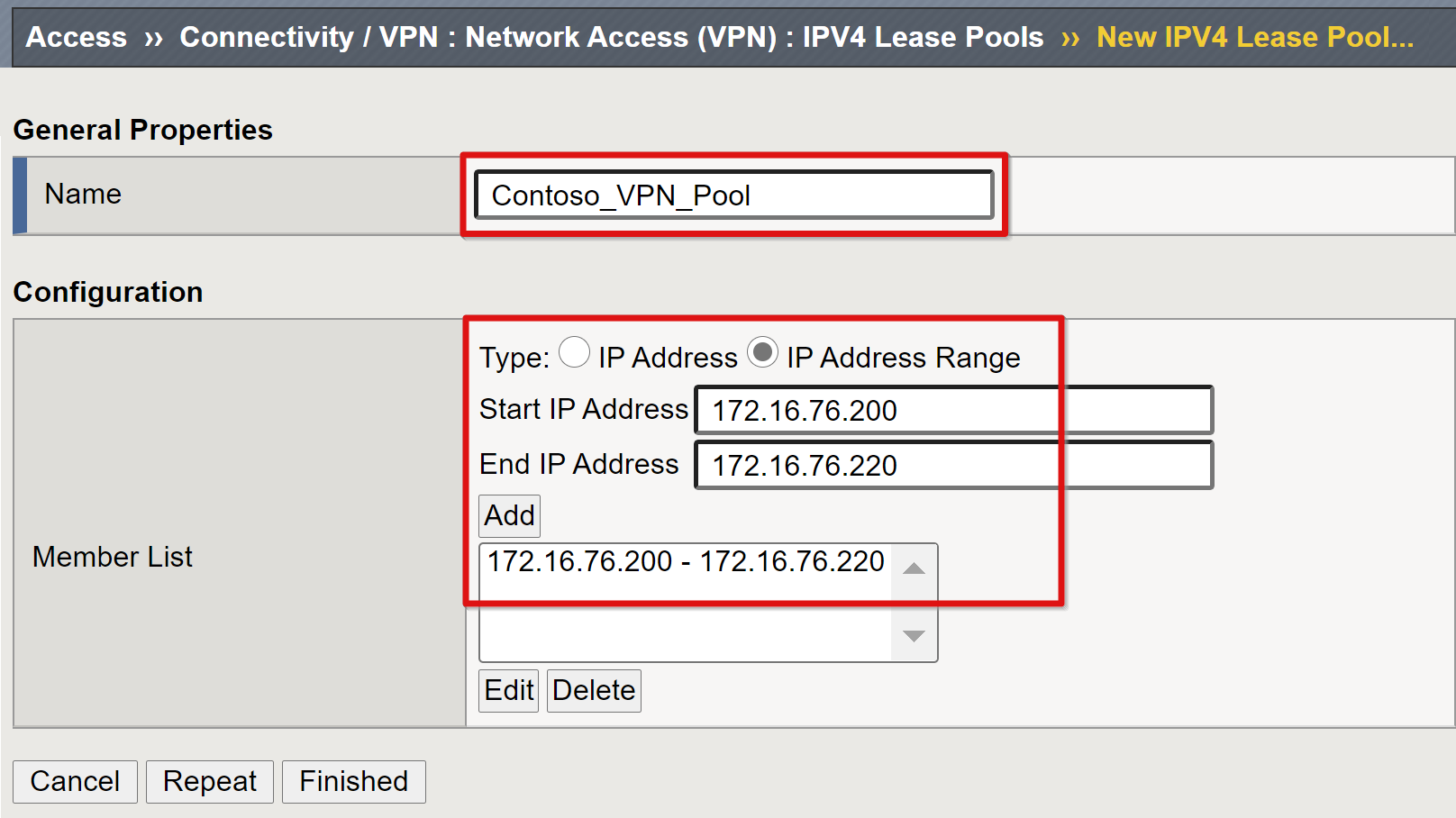
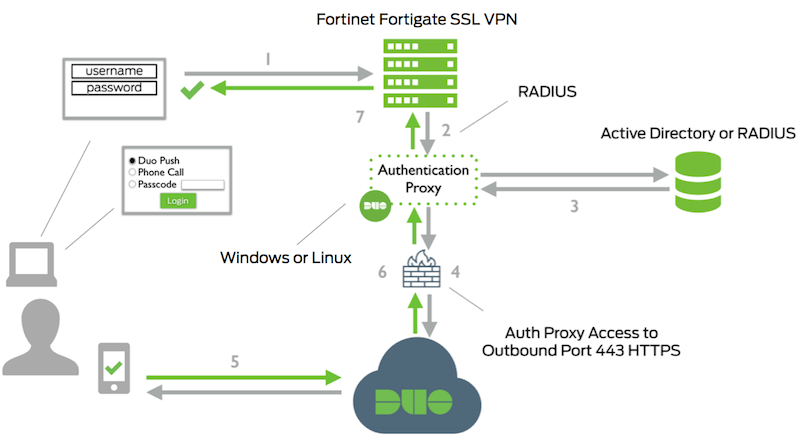
ConfiguringSSLVPNfora full tunnel deployment involves enabling theSSLVPNfeature on thenetworkinterface, setting up user authentication and groups, creating anSSLVPNweb portal, and mapping authentication/portal settings for user groups . It also includes setting up firewall policies to allow or restrict traffic through the tunnel, ensuring all user traffic goes through the corporate ...
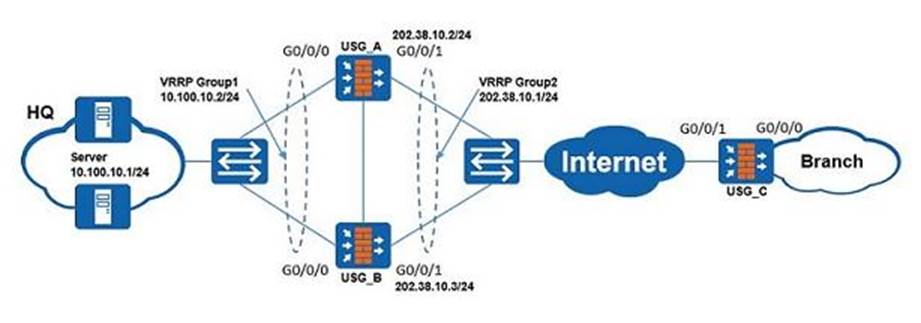
Jan 5, 2026This style ofVPNrequires a dedicated subnet for the OpenVPN interconnection betweennetworksin addition to the subnets on both ends. Figure OpenVPN Example Site-to-SiteSSL/TLSNetworkshows a depiction of this layout, using 10.3.101.0/24 as the IPv4 TunnelNetworkfortheVPN.

Remote AccessVPNProducts Remote access is integrated into every Check Pointnetworkfirewall. Configure client-to-siteVPNor set up anSSLVPNPortal to connect from any browser.
2 days agoExplore the essentials of configuring a Japan eSIM for business travel. Learn how to set up a secureVPNand hotspot, ensuring seamless connectivity and data protection. This guide provides step-by-step instructions to help business travelers maintain communication and productivity while abroad.
TheSSLVPNgateway and contextconfigurationmust be completed before a remote user can access resources on a privatenetworkbehind anSSLVPN.Formore information, see the " How to ConfigureSSLVPNServices on a Router" section.
In this video tutorial, you will learn how to configure and set up anSSLVPNconnection on a FortiGate Firewall. The step-by-step guide will show you how to create user accounts, configure the ...
🚀SSLVPNConfigurationin Sophos Firewall Today, I configuredSSLVPNin Sophos Firewall to enable secure remote access to internalnetworkresources. 🔹 CreatedVPNusers and groups 🔹 ...
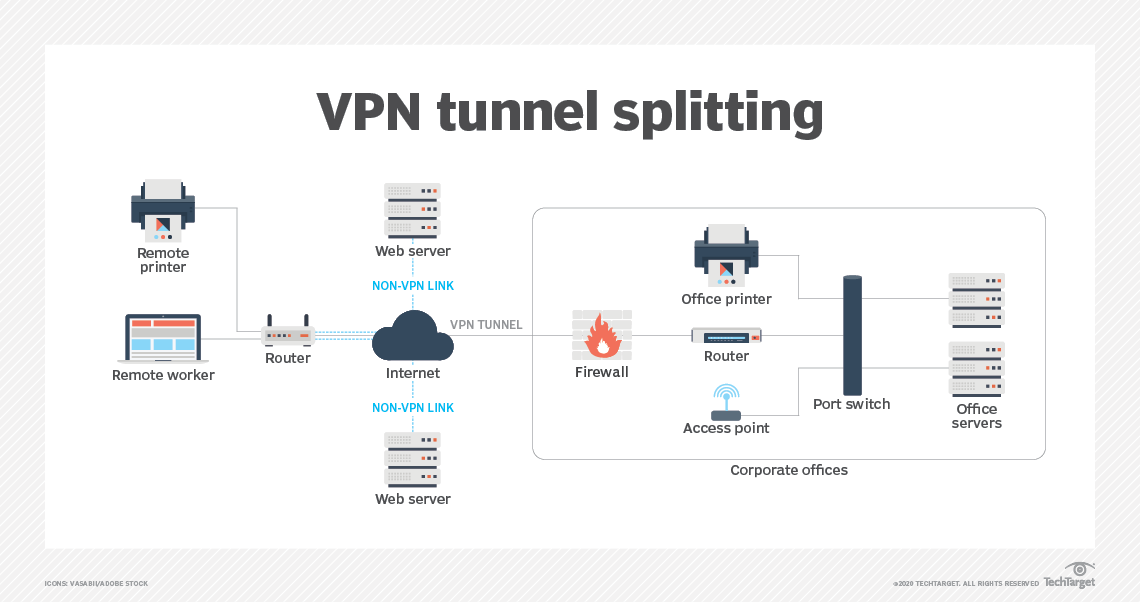
Virtual privatenetworkVPNconnectivity overview, showing intranet site-to-site and remote-workconfigurationsused together A virtual privatenetwork(VPN) is an overlaynetworkthat usesnetworkvirtualization to extend a privatenetworkacross a publicnetwork, such as the Internet, via the use of encryption and tunneling protocols. [1]
When everything has been tested, adding authentication via client certificates, if necessary, can be added to theconfiguration. To authenticate devices with a third-partyVPNapplication, check "Enable X-Auth Support" in the gateway's ClientConfiguration. Group Name and password must be configured for this setting.

Annetworkengineer is configuringSSLForward Proxy decryption on a Palo AltoNetworksfirewall. The company's internal clients trust a corporate root certificate authority (CA). To ensure the firewall can properly validate the certificates of external web servers, the engineer must configure a specific component.

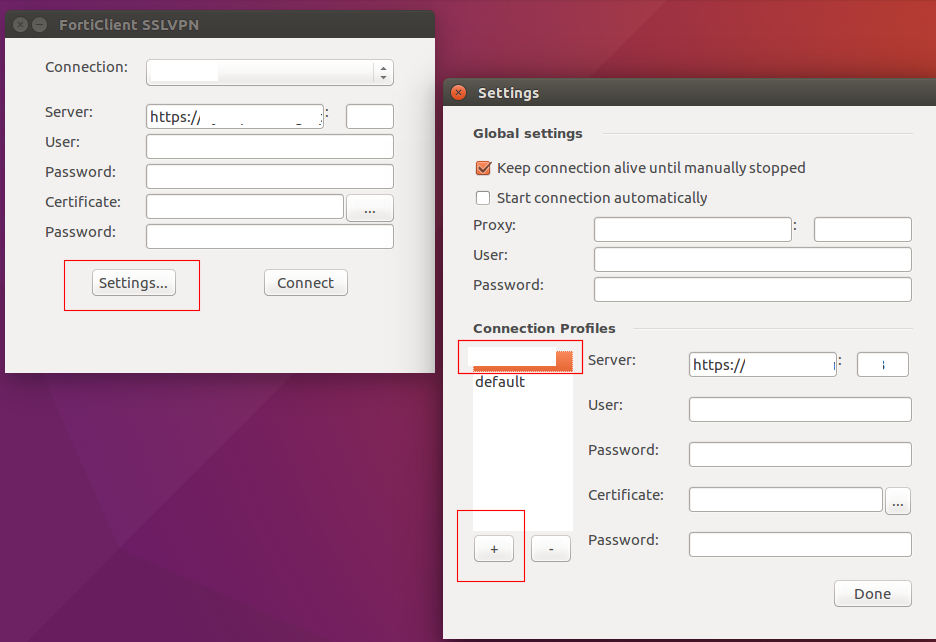
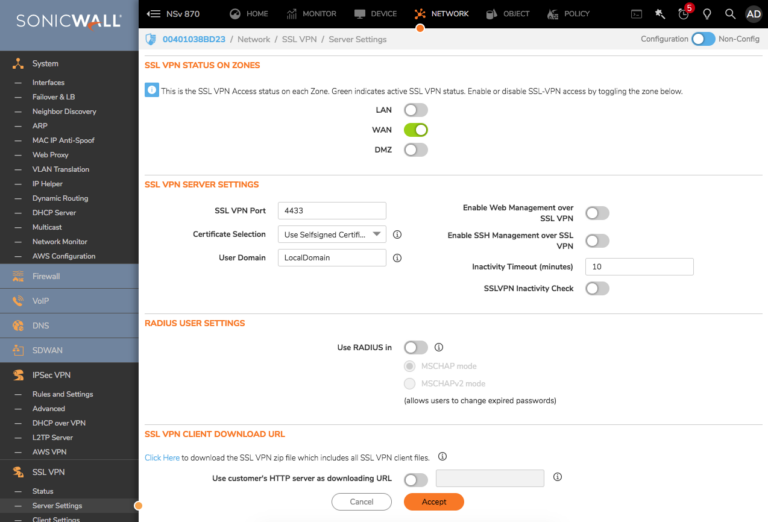
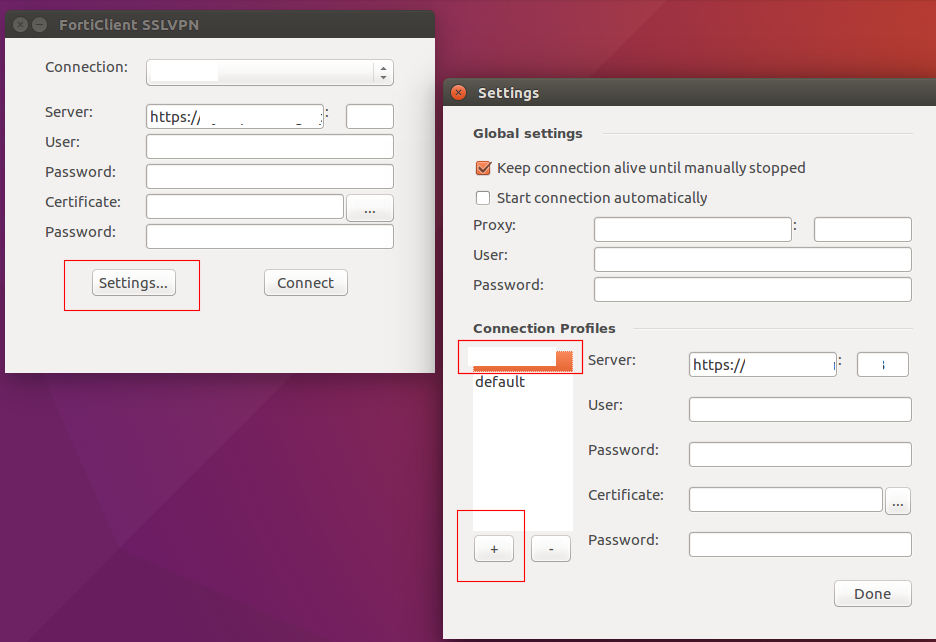
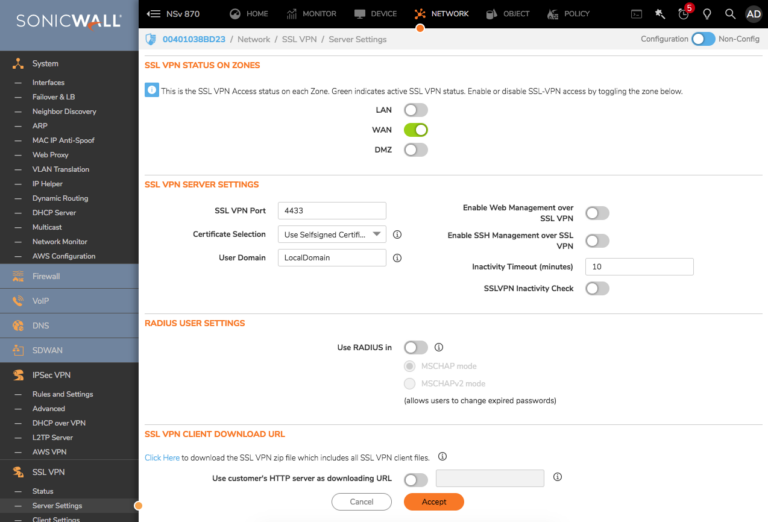
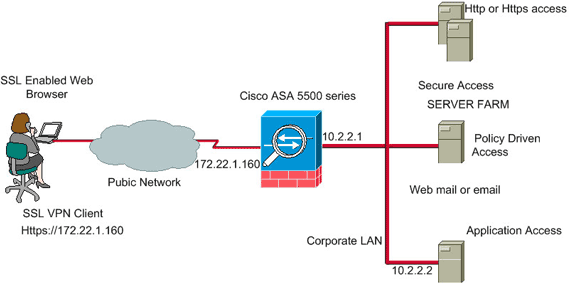
SSLVPNis one method of allowing remote users to connect to the SonicWall and access the internalnetworkresources.SSLVPNconnections can be setup with

AnyConnect Secure Mobility Client v4.x: Get product information, technical documents, downloads, and community content.
Nov 22, 2024Setting up a Virtual PrivateNetwork(VPN) using Fortinet's FortiGate firewall enhances secure remote access to yournetwork. This comprehensive guide will walk you through configuring bothSSLVPNand IPsecVPN, utilizing Fortinet's resources and best practices.

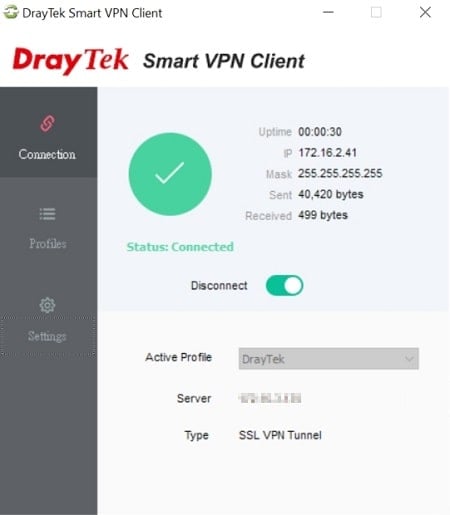
SSLVPNVirtual PrivateNetwork(VPN) technology lets remote users connect to private computernetworksto gain access to their resources in a secure way. For example, an employee traveling or working at home can use aVPNto securely access the officenetworkthrough the internet.