TP-Link G Router Setup for Advanced Security: A Comprehensive Guide
In today's digital age, having a secure and reliable home network is crucial for protecting your personal data and preventing unauthorized access. TP-Link, a leading manufacturer of networking equipment, offers a range of routers that cater to different needs and budgets. In this article, we will delve into the TP-Link G router setup for advanced security, providing you with a step-by-step guide on how to configure your router for optimal performance and security.
Why Advanced Security Matters
Your home network is a potential entry point for hackers and malicious actors, who can exploit vulnerabilities to gain unauthorized access to your sensitive information. By setting up advanced security features on your TP-Link G router, you can significantly reduce the risk of cyber threats and ensure a safe browsing experience for all devices connected to your network.
Understanding Your TP-Link G Router

Before we dive into the setup process, it's essential to familiarize yourself with your TP-Link G router's features and capabilities. Your router likely comes with a user manual or a quick start guide that provides an overview of its settings and configuration options. Make sure to read through the documentation to understand the various settings and features available on your router.
Step 1: Initial Setup
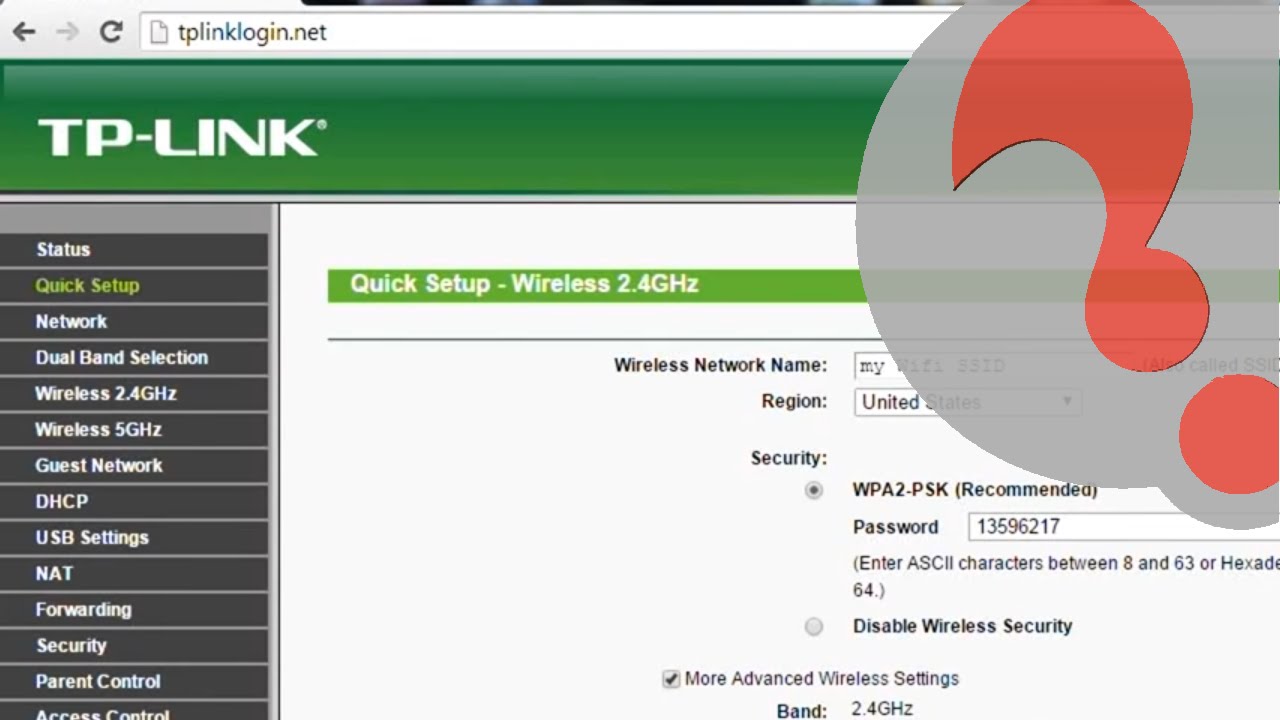
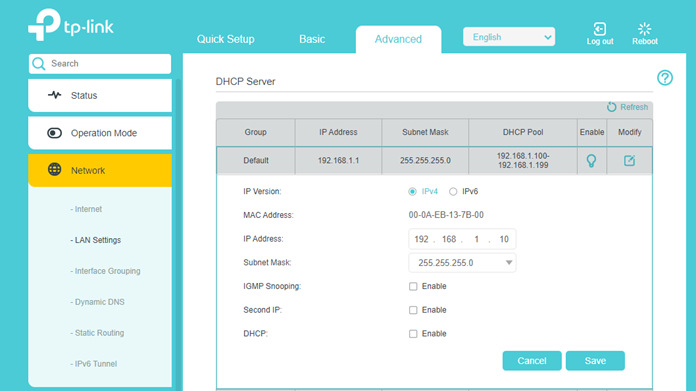
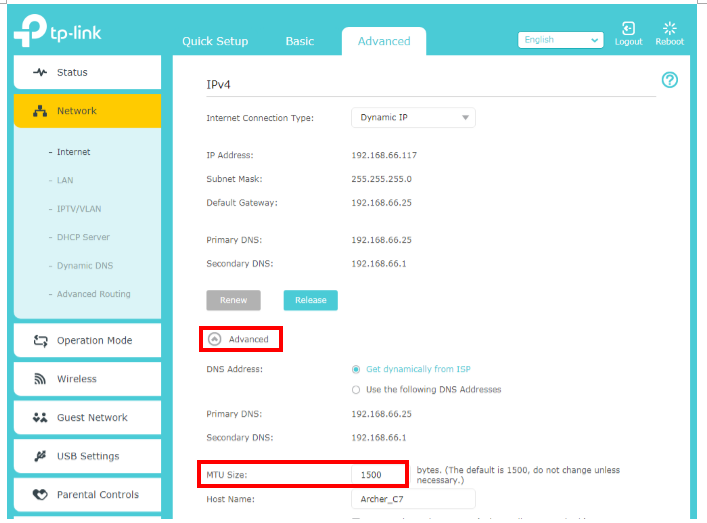
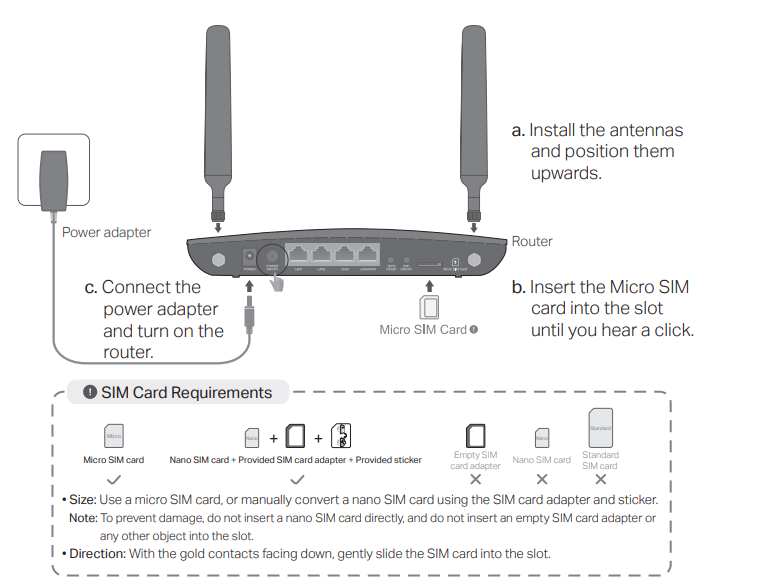
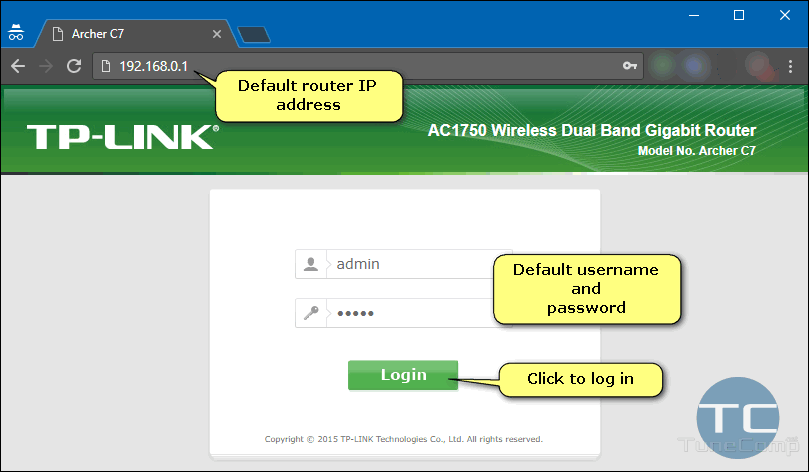
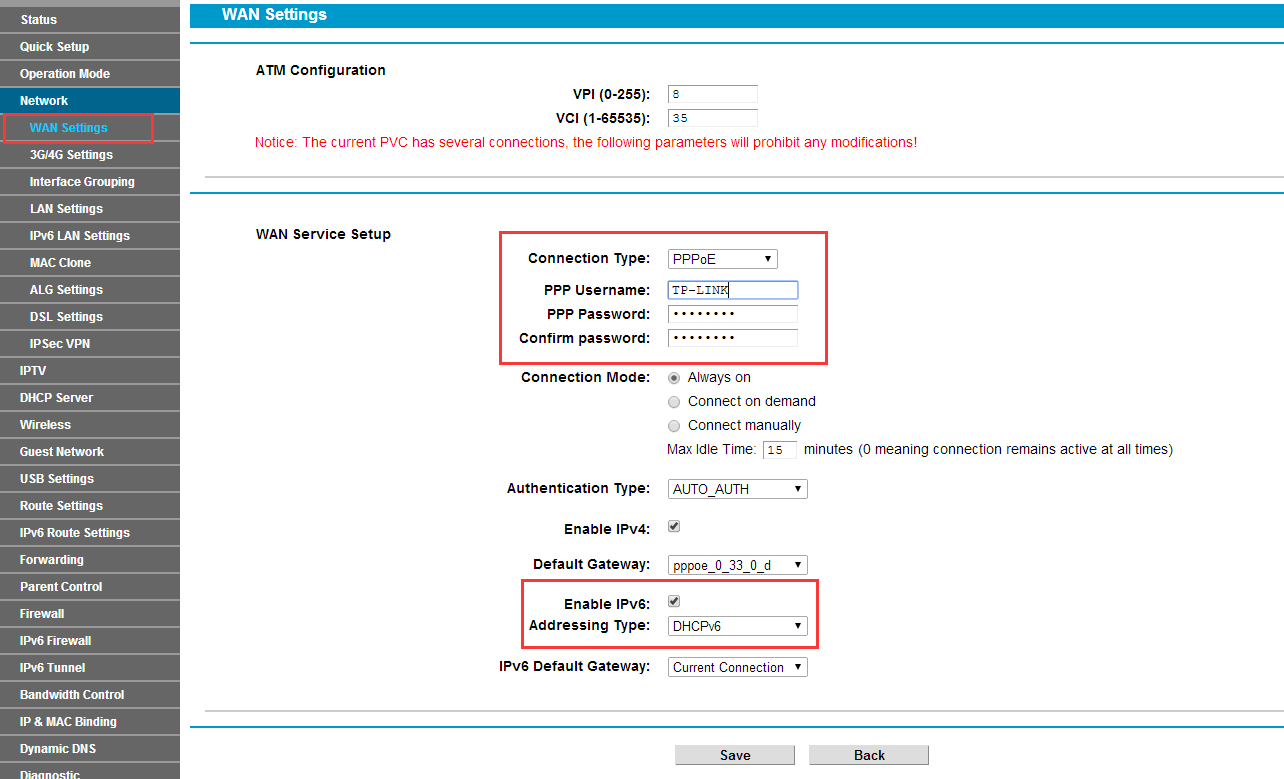
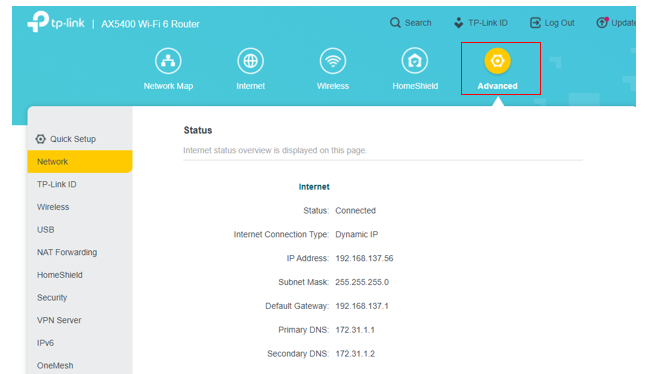
Begin by physically setting up your router, following the manufacturer's instructions for cable connections and power supply. Once your router is powered on, access the web-based interface by typing the router's IP address in a web browser. The default IP address is usually 192.168.0.1 or 192.168.1.1. Log in to the interface using the default administrator username and password, which can be found in the user manual or on the underside of the router.
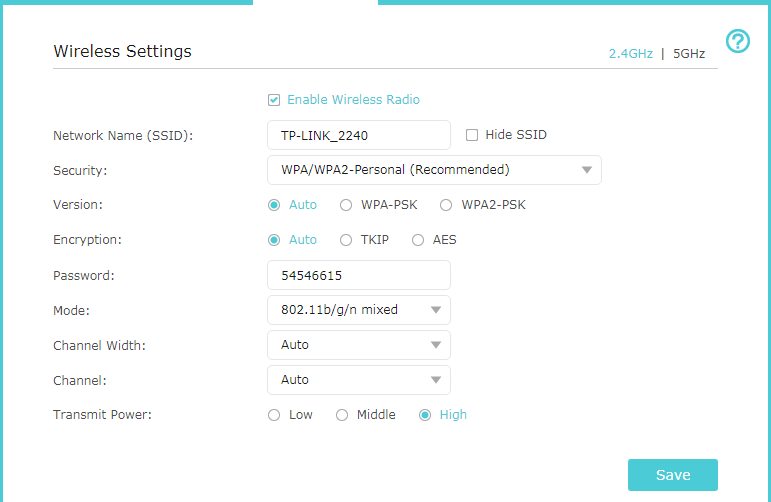
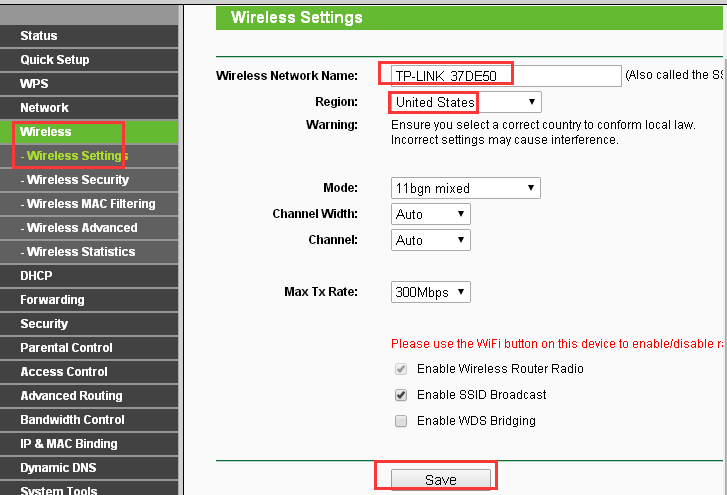
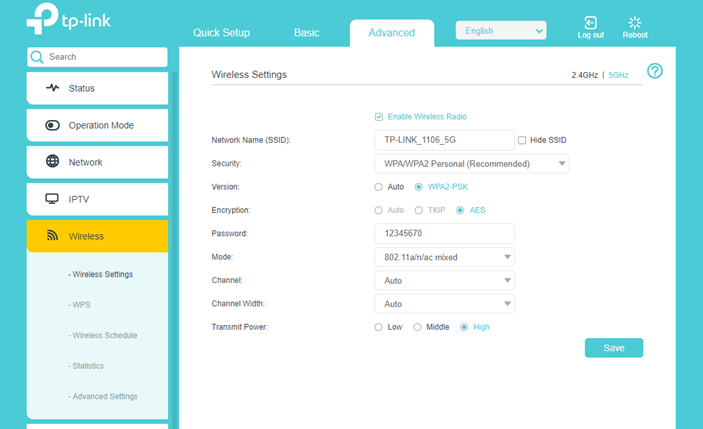
Configure your router's wireless settings to ensure secure and stable connections. Change the default network name (SSID) and password to prevent unauthorized access. Choose a strong password that includes a mix of uppercase and lowercase letters, numbers, and special characters. Enable WPA3 encryption for advanced security, which provides protection against brute-force attacks and eavesdropping.
Such details provide a deeper understanding and appreciation for Tp-Link G Router Setup For Advanced Security.
Step 3: Firewall and Security Settings
Create a guest network to isolate visitors and IoT devices from your main network. Configure the guest network's SSID and password, and set up a separate firewall rule to block incoming traffic on the guest network. Additionally, enable WPA3 encryption on the guest network for advanced security. When connecting IoT devices to your network, use the WPS (Wi-Fi Protected Setup) feature to simplify the process and reduce the risk of security breaches.
Step 5: Regular Updates and Maintenance
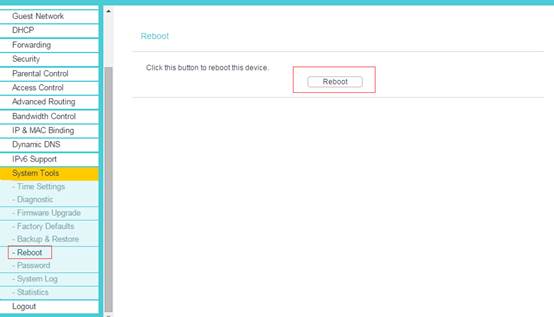
Regularly update your router's firmware to ensure you have the latest security patches and features. Perform routine maintenance tasks, such as resetting the router to its default settings, to maintain optimal performance and security. Monitor your network for suspicious activity and adjust your security settings as needed to prevent potential threats.

Conclusion
Additional Tips and Resources
- Consult your router's user manual or online documentation for specific instructions and settings.
- Change your router's default administrator username and password to prevent unauthorized access.
- Use a strong password that includes a mix of uppercase and lowercase letters, numbers, and special characters.
- Enable WPA3 encryption for advanced security and protection against brute-force attacks and eavesdropping.
- Regularly update your router's firmware to ensure you have the latest security patches and features.
- Perform routine maintenance tasks, such as resetting the router to its default settings, to maintain optimal performance and security.
For more information and resources, visit the TP-Link website or consult with a networking expert. Remember to stay vigilant and adapt to changing security threats to ensure your home network remains secure and reliable.

_20240830055723o.jpg)