Encryption Best Practices for Users: Protecting Your Digital Assets
In today's digital landscape, data breaches and cyber threats continue to rise at an alarming rate, with organizations of all sizes finding themselves vulnerable to increasingly sophisticated attacks. As a user, it's essential to implement robust encryption practices to protect your digital assets. This article provides a comprehensive guide to encryption best practices for users, including selecting appropriate encryption methods, implementing strong key management strategies, and maintaining up-to-date systems.Why Encryption is Essential for Users
Such details provide a deeper understanding and appreciation for Encryption Best Practices For Users.
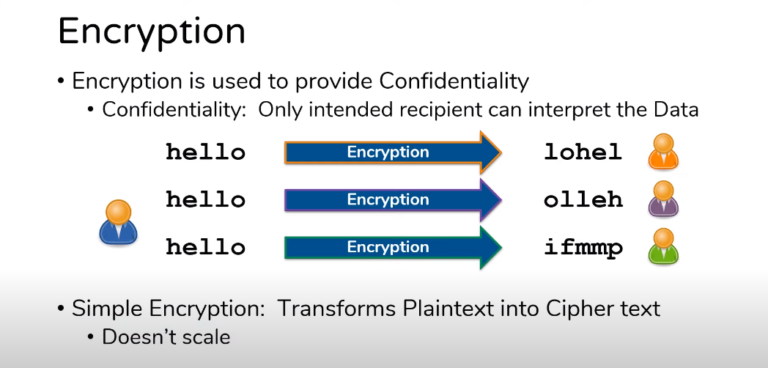
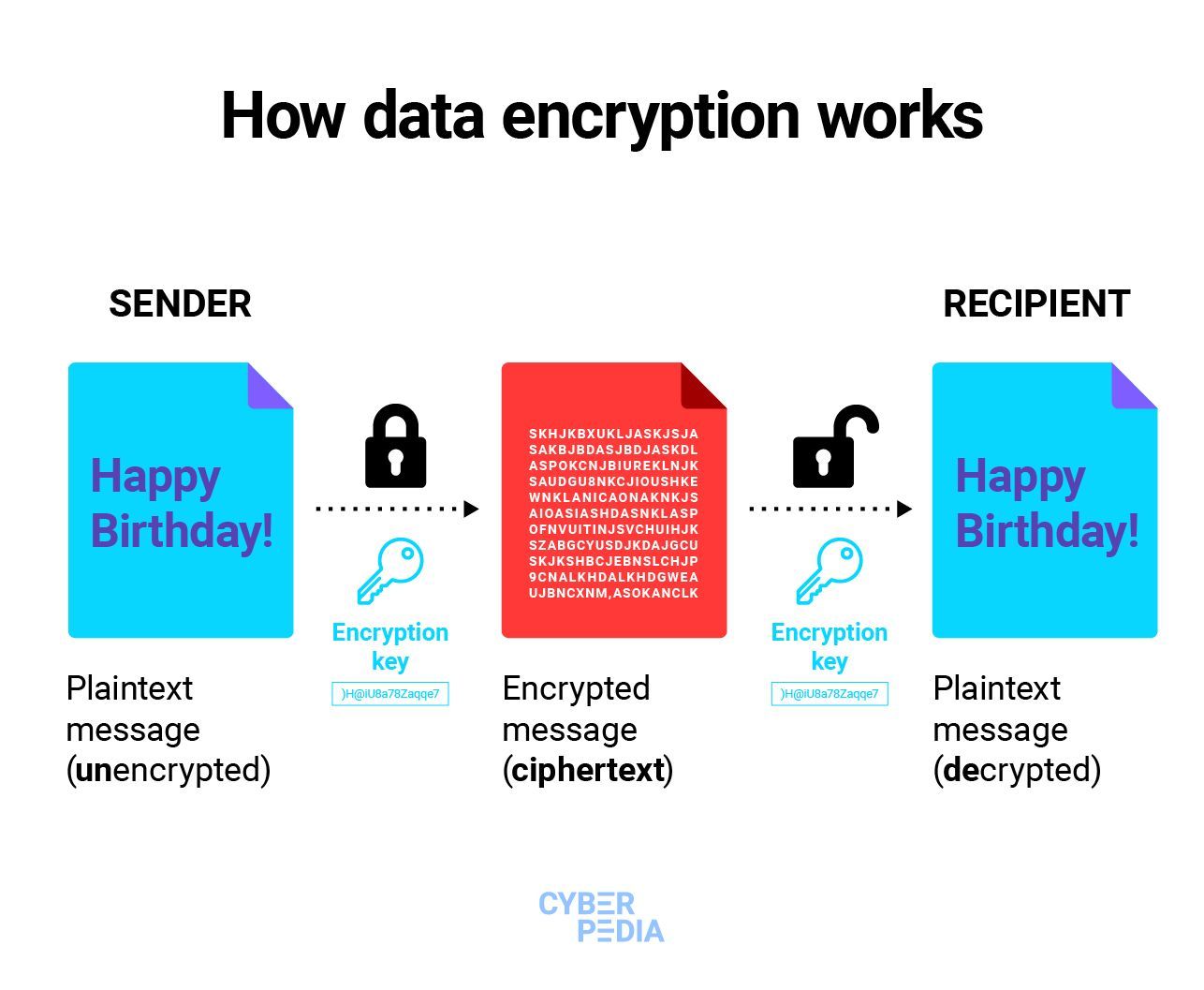
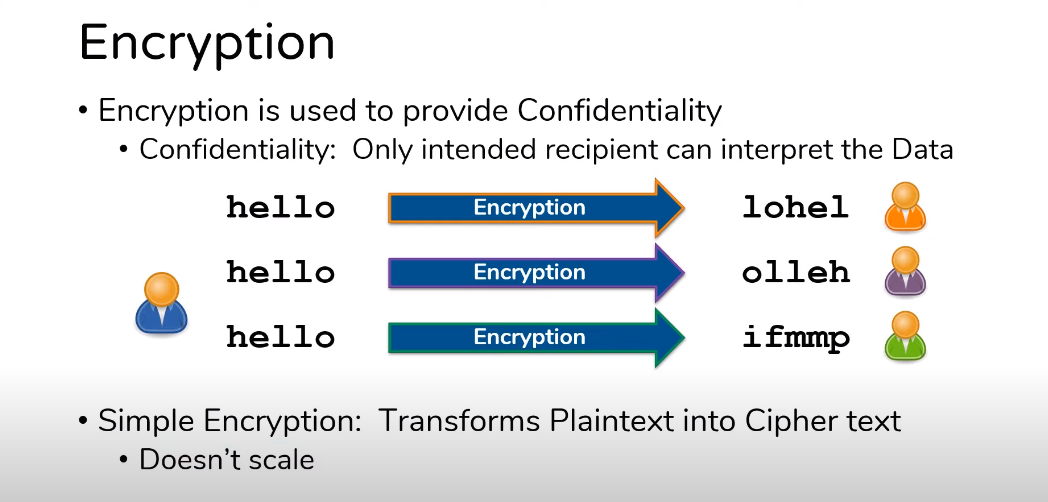
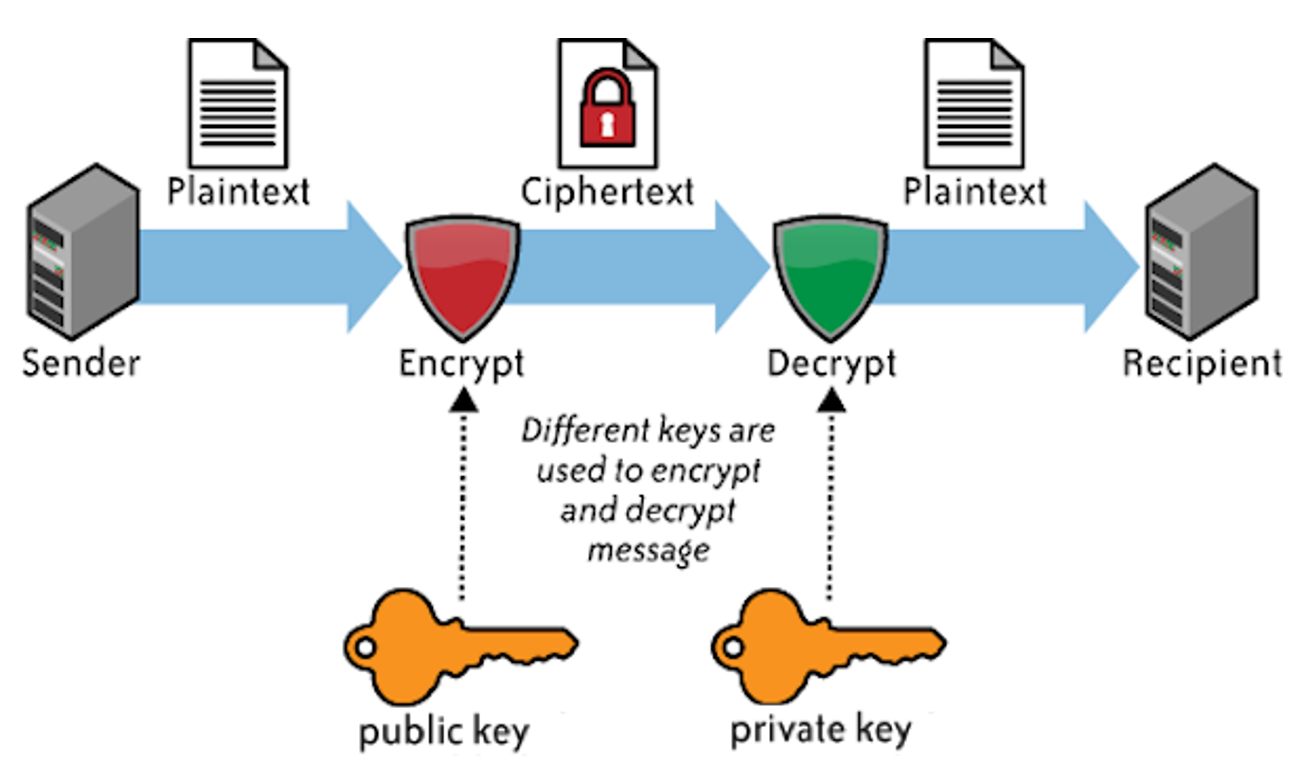
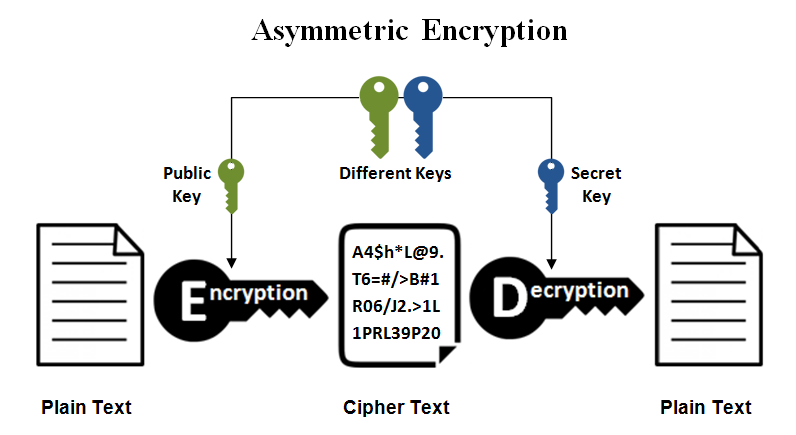
Data encryption is the process of converting plaintext data into unreadable ciphertext to protect it from unauthorized access. Encryption ensures that only authorized users can access sensitive information, making it a critical component of robust data security. By prioritizing encryption, users can safeguard their digital assets and prevent data breaches.Encryption Best Practices for Users

As we can see from the illustration, Encryption Best Practices For Users has many fascinating aspects to explore.
Here are some essential encryption best practices for users:- Select Appropriate Encryption Methods: Choose encryption algorithms that meet your security needs, such as AES-256 for symmetric encryption and RSA/ECC for asymmetric encryption.
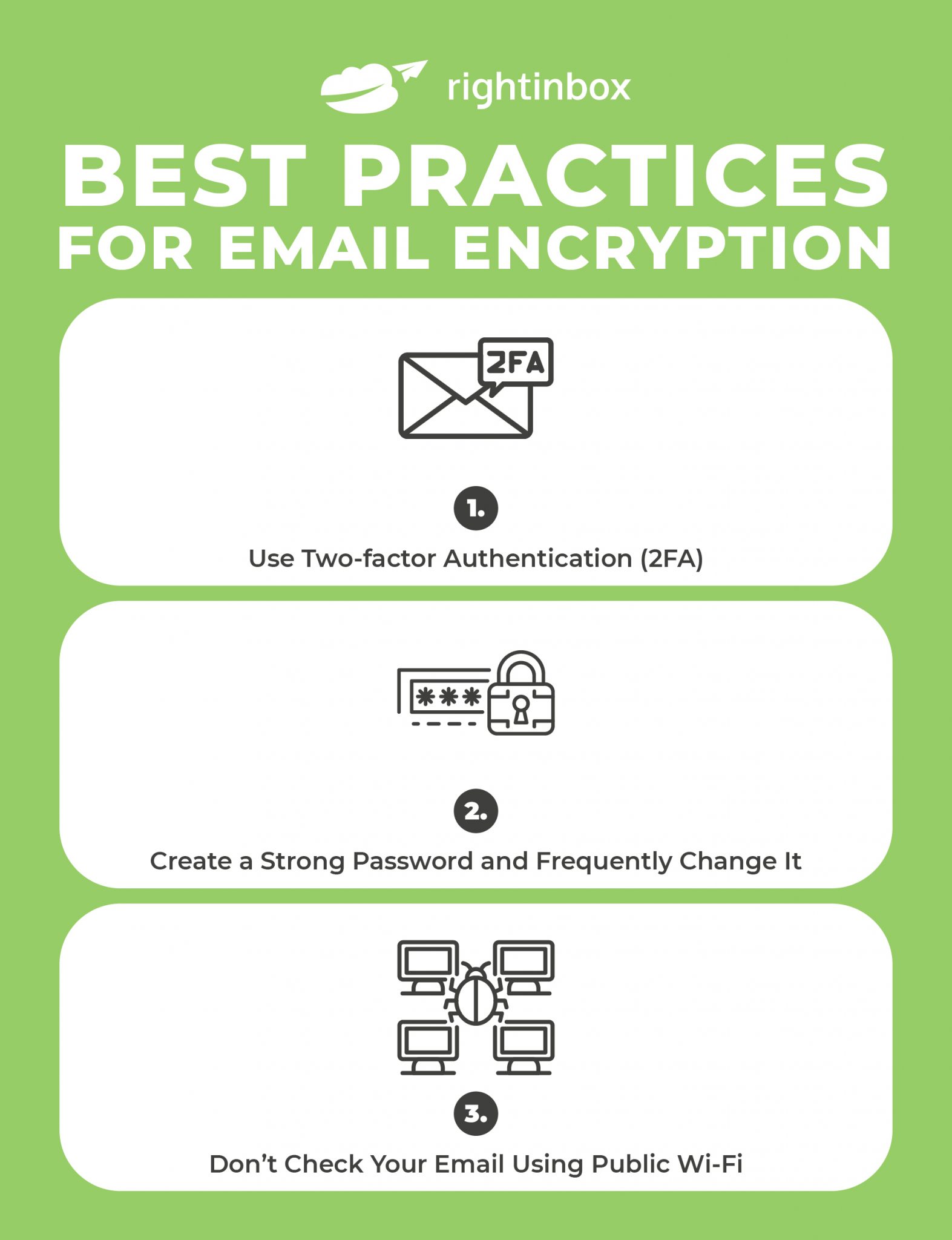
- Implement Strong Key Management Strategies: Use strong, complex keys for encryption, and store them securely using hardware security modules (HSMs) or key management systems.
- Maintain Up-to-Date Systems: Regularly update your operating system, browser, and other software to ensure you have the latest security patches and features.
- Use Established Encryption Algorithms: Stick to well-established encryption algorithms, such as AES-256, and avoid custom or proprietary ciphers.
- Use Strong Authentication and Authorization: Implement strong authentication and authorization mechanisms to ensure that only authorized users can access encrypted data.
- Regularly Test and Audit Encryption Implementations: Test and audit your encryption implementations regularly to ensure they function correctly and remain secure.

As we can see from the illustration, Encryption Best Practices For Users has many fascinating aspects to explore.
In addition to the above best practices, users should also consider the following:- Use Password-Based Key Derivation Functions (PBKDFs): Use PBKDFs to securely store passwords and other sensitive information.
- Enable Perfect Forward Secrecy (PFS): Enable PFS to ensure that encrypted sessions are secure and cannot be compromised even if an attacker obtains a master key.
- Use Secure Communication Protocols: Use secure communication protocols, such as HTTPS and SSH, to protect data in transit.
- Regularly Back Up Encrypted Data: Regularly back up encrypted data to prevent loss or corruption.